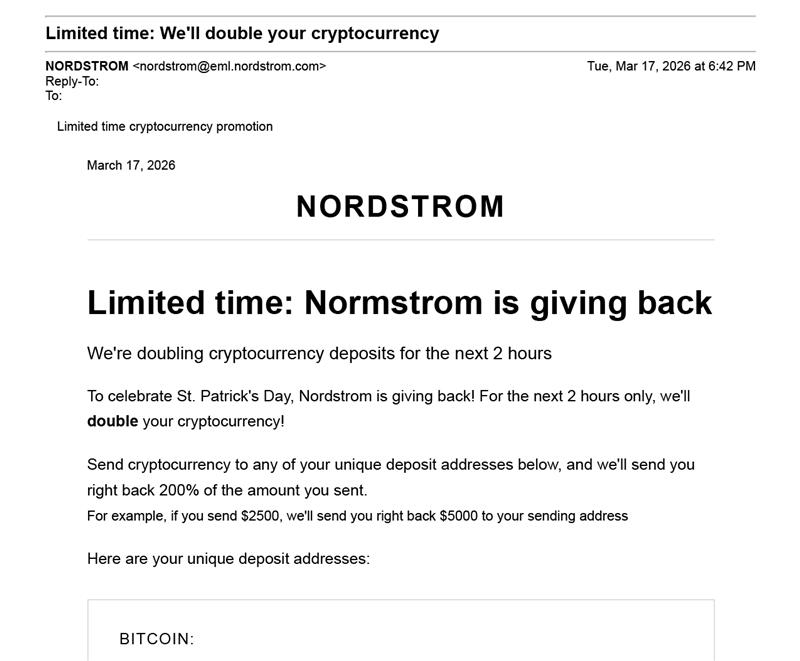
It arrived in a customer’s inbox looking like any other promotional email from a major retailer. The branding was polished, the formatting familiar, and the sender appeared to be Nordstrom. The message offered a limited-time opportunity (2 hours): deposit funds into one of three designated cryptocurrency wallets, and Nordstrom would double the deposit as part of a new customer rewards program. The catch, of course, was that Nordstrom had nothing to do with it.
The email was a scam—a well-executed example of a growing category of fraud that exploits consumer trust in recognizable brands and pairs it with the perceived complexity and legitimacy of cryptocurrency.
The real email – we’ve redacted some identifying details for recipient privacy and reader security.
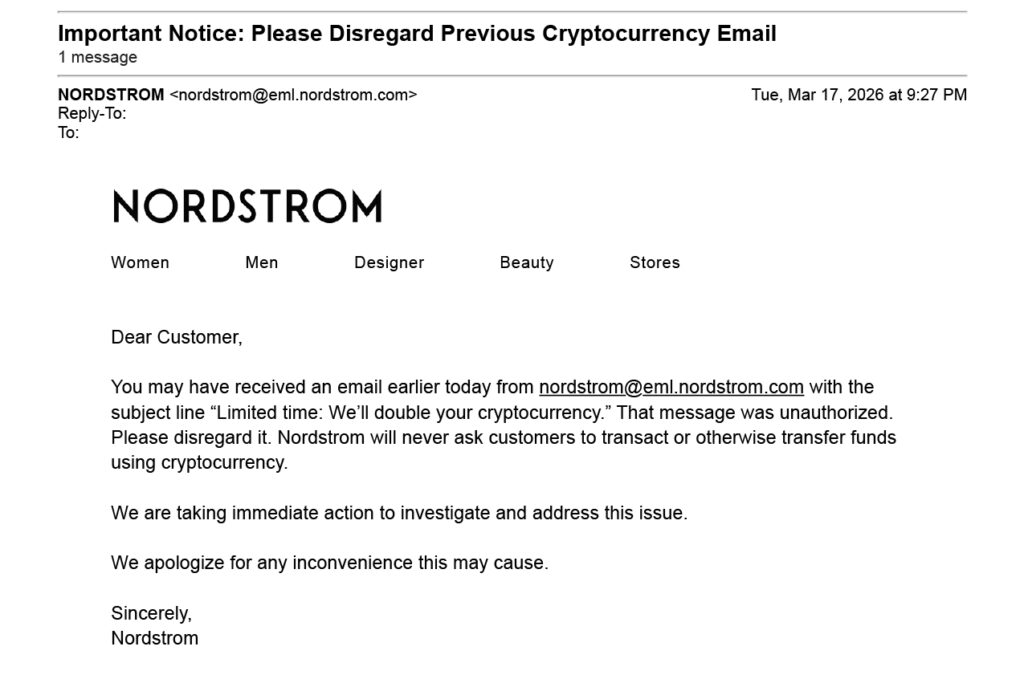
Within a couple of hours, Nordstrom sent a follow-up email to customers warning them that the original message was fraudulent and urging them not to engage with it or send funds to any of the listed wallets. The company’s swift response likely prevented additional losses, but for anyone who acted before the warning arrived, the damage was already done.
These schemes are becoming more common and more convincing. Understanding how they work, what warning signs to look for, and what tools exist to investigate them is increasingly important for consumers, companies, and risk management professionals alike.
The Anatomy of a Crypto Deposit Scam
The structure of the Nordstrom impersonation email follows a well-established pattern. Fraudsters create emails that closely mimic the visual identity of a trusted brand—logo, color scheme, layout, and tone—to lower the recipient’s guard. The call to action introduces cryptocurrency, which lends an air of sophistication and novelty that can obscure the underlying simplicity of the scheme: send us money, and we’ll send you more back.
In this case, the email directed recipients to deposit funds into three separate crypto wallets, likely to disperse incoming funds and make tracing more difficult. Splitting deposits across multiple wallets is a common tactic that complicates recovery and creates layered transaction trails across the blockchain.
The promise of doubled deposits is a classic hallmark of what’s known as an advance-fee or “multiplier” scam—a concept as old as fraud itself, repackaged for the digital asset era.
These scams succeed in part because cryptocurrency transactions are irreversible. Unlike a credit card charge that can be disputed or a wire transfer that a bank may be able to recall, once crypto is sent to an external wallet, there is no built-in mechanism to claw it back. Fraudsters rely on this finality.
Red Flags That Signal a Scam
While the presentation may be convincing, crypto scams almost always share identifiable characteristics. Being alert to these red flags can prevent significant financial loss.
- Too good to be true: Any offer that promises guaranteed returns or the multiplication of deposited funds is suspicious. No legitimate company—retailer or otherwise—will offer to double a cryptocurrency deposit. If an offer sounds too good to be true, it almost certainly is.
- Sense of urgency: Scam emails frequently impose tight deadlines or claim that the offer is available only to a limited number of participants. The intent is to pressure recipients into acting before they have time to think critically or verify the offer’s legitimacy.
- Sender verification: While an email may display a familiar brand name, the actual sending address often reveals the deception. A message purporting to be from a legitimate sender but sent from a domain that doesn’t match the official communications infrastructure is a strong signal that something is wrong. Recipients should hover over or inspect the sender address carefully before engaging.
- Crypto as a catalyst: Major retailers do not conduct customer promotions through decentralized crypto wallets. The presence of wallet addresses in a promotional email is itself a red flag.
- Errors and inconsistencies: Poor grammar, misspellings, unusual phrasing, slightly off branding, and links that redirect to unfamiliar URLs are all signals that an email may not be what it appears.
- Lack of awareness: Legitimate companies communicate major promotions across multiple channels—their website, social media, and in-store signage. If the only evidence of a promotion is a single unsolicited email, that alone warrants skepticism.
How Investigators Trace Crypto Fraud
When fraud does occur, the investigation often begins with the blockchain itself. Because most major cryptocurrencies operate on public ledgers, every transaction—while pseudonymous—is permanently recorded and visible. This creates a detailed trail that trained investigators can analyze, even when bad actors attempt to obscure the flow of funds.
Blockchain analytics platforms allow investigators to map the movement of cryptocurrency across wallets, identify clusters of related addresses, and flag connections to known illicit actors, sanctioned entities, or darknet marketplaces. These tools can visualize complex transaction networks and trace funds through multiple hops, mixers, and exchanges. But technology alone rarely tells the full story. Effective crypto investigations require pairing blockchain analytics with the kind of traditional asset tracing expertise that has long been central to forensic accounting and financial investigations.
Asset tracing—the discipline of “following the money” to determine where it originated, how it moved, and where it ultimately came to rest—applies to digital assets much the same way it applies to conventional funds. The core principles are the same: identify the flow, document the chain of custody, and connect pseudonymous transactions to real-world actors and accounts. Investigators experienced in tracing assets across complex corporate structures, offshore accounts, and layered financial transactions bring critical skills to crypto cases, where funds often pass through multiple wallets, cross between blockchain networks, and convert between different digital and fiat currencies before reaching their destination.
Investigators leverage this asset tracing foundation to the digital asset environment, combining blockchain analytics with open-source intelligence research, financial record analysis, and coordination with law enforcement to build comprehensive pictures of how funds moved and who controlled them. This convergence of traditional forensic accounting and digital asset investigation has become essential as cryptocurrency features more prominently in fraud, money laundering, sanctions evasion, and asset concealment cases.
Investigators also work with cryptocurrency exchanges, which are often the on-ramp or off-ramp for illicit funds. Exchanges that comply with anti-money laundering regulations maintain know-your-customer records that can help link wallet addresses to real-world identities. When a scam’s proceeds flow through a regulated exchange, investigators have a meaningful opportunity to identify the individuals behind the scheme.
The investigative toolkit continues to evolve. Advances in machine learning and pattern recognition are improving the ability to detect suspicious transaction behavior in real time, and cross-chain analytics are addressing the challenge of tracing funds that move between different blockchain networks. These capabilities are especially important as fraudsters grow more sophisticated in their methods of obfuscation.
Protecting Yourself and Your Organization
The Nordstrom impersonation email is a reminder that crypto scams don’t always look like crypto scams. They often arrive disguised as familiar, trustworthy communications—and their effectiveness depends on recipients not pausing to question what they’re seeing.
For individuals, the best defense remains skepticism toward unsolicited offers, careful verification of sender information, and a simple rule: never send cryptocurrency in response to an unexpected request, regardless of how legitimate it appears. For organizations, the incident underscores the importance of brand monitoring, consumer education, and having investigative resources in place to respond quickly when impersonation occurs.
As cryptocurrency adoption continues to grow, so too will the creativity and persistence of those who seek to exploit it. Staying informed about common fraud tactics—and knowing that sophisticated tools exist to investigate and trace illicit transactions—puts both consumers and organizations in a stronger position to recognize scams before they cause harm and pursue accountability when they do.
The views expressed in this article are those of the authors and do not necessarily reflect the views of StoneTurn, Province, or its affiliates. All trademarks and brand references (including Nordstrom) are used solely for descriptive and informational purposes. This article does not constitute legal, financial, or investigative advice.
If you have any questions or would like to discuss how StoneTurn can help, reach out to David Burroughs or Kyla Curley.
To receive StoneTurn Insights, sign up for our newsletter.